Authentication vs Authorization: The Complete Backend Security Architecture Guide
A comprehensive, in-depth guide explaining authentication and authorization, implementation strategies, security architecture, OAuth flows, RBAC, Zero Trust, and real-world backend examples.
Authentication vs Authorization
Modern applications handle sensitive data, financial transactions, and private user information. Securing these systems requires a clear separation between identity verification and access control.
Authentication and Authorization are often confused — but architecturally, they serve very different purposes.
- Authentication → Who are you?
- Authorization → What can you do?
Understanding their differences is critical when building scalable backend systems.
Why This Distinction Matters
Many security vulnerabilities occur because developers mix authentication logic with authorization checks. A system might correctly identify a user but fail to enforce permission boundaries.
This leads to:
- Privilege escalation
- Data leaks
- Broken access control
- Unauthorized resource modification
Security architecture must separate identity from permissions.
Authentication and authorization layered architecture
Deep Dive: Authentication
Authentication verifies identity using credentials or cryptographic proof.
Authentication Factors
- Something you know – Password
- Something you have – OTP device, phone, hardware key
- Something you are – Biometrics
Modern Authentication Methods
- JWT-based authentication
- OAuth 2.0
- OpenID Connect
- Passwordless login
- Magic links
- WebAuthn
Example of issuing JWT:
import jwt from 'jsonwebtoken';
const token = jwt.sign(
{ userId: user._id, role: user.role },
process.env.JWT_SECRET,
{ expiresIn: '15m' }
);
Session-Based vs Token-Based Authentication
| Session-Based | Token-Based |
|---|---|
| Stored on server | Stateless |
| Uses cookies | Uses Authorization header |
| Harder to scale | Easily scalable |
Modern microservices prefer token-based authentication.
Deep Dive: Authorization
Authorization determines what resources an authenticated user can access.
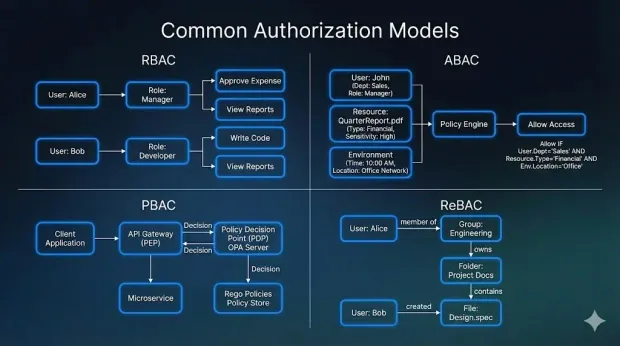
Common Models
1. RBAC (Role-Based Access Control)
Roles define permissions.
2. ABAC (Attribute-Based Access Control)
Uses dynamic attributes like department, region, or time.
3. PBAC (Policy-Based Access Control)
Centralized policy engines evaluate access.
Example Middleware:
function authorize(requiredRole) {
return (req, res, next) => {
if (req.user.role !== requiredRole) {
return res.status(403).json({ message: 'Forbidden' });
}
next();
};
}
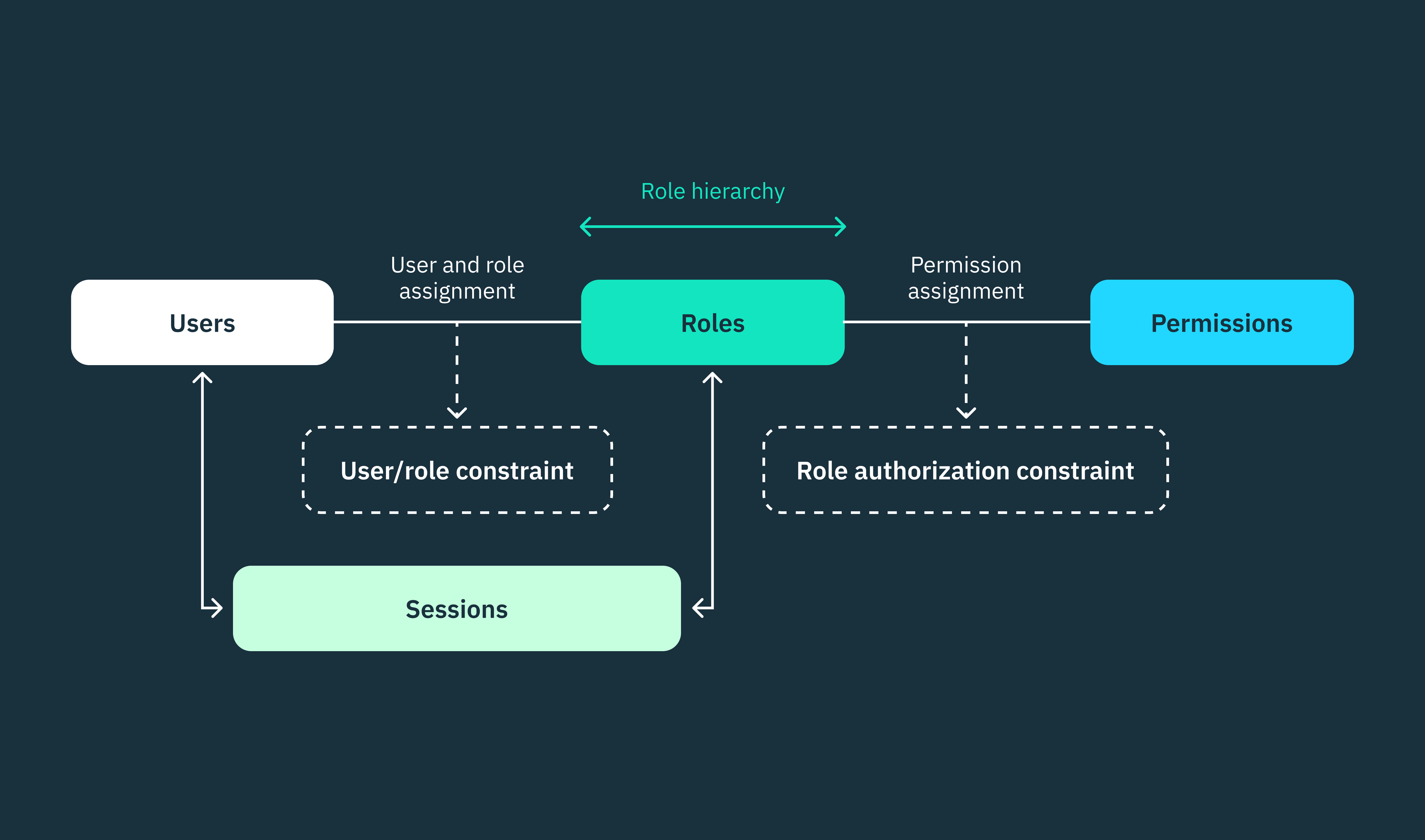
RBAC access control diagram
OAuth 2.0 Flow Overview
OAuth allows third-party apps to access resources without exposing credentials.
Authorization Code Flow
- User redirected to authorization server
- User logs in
- Server returns authorization code
- Backend exchanges code for access token
This separates authentication from authorization scopes.
Microservices Architecture Consideration
In distributed systems:
- API Gateway validates authentication
- Services verify token signature
- Authorization handled per service
Never trust internal network blindly.
Adopt Zero Trust Architecture principles.
Common Security Vulnerabilities
- Broken Access Control
- IDOR (Insecure Direct Object References)
- Token replay attacks
- Privilege escalation
- Missing role validation
Mitigation strategies include:
- Token expiration
- Refresh token rotation
- Least privilege enforcement
- Permission checks on every request
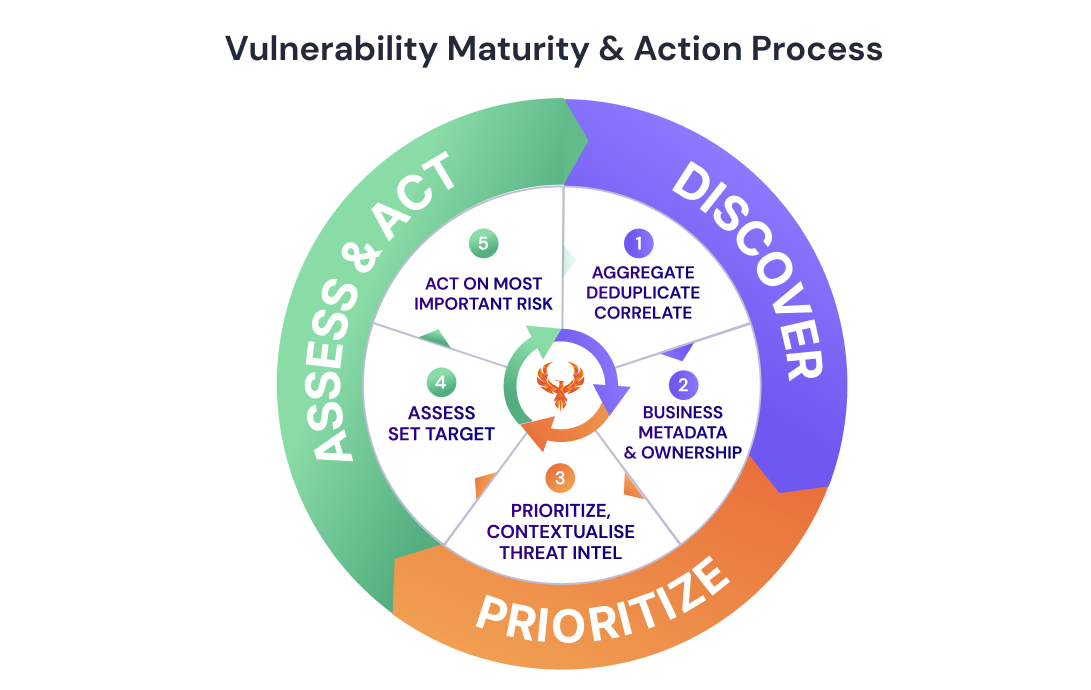
Security vulnerability flow diagram
401 vs 403 Explained
- 401 Unauthorized → Authentication required or invalid.
- 403 Forbidden → Authenticated but lacks permission.
Properly distinguishing these improves API clarity and debugging.
Enterprise Best Practices
- Enforce HTTPS everywhere
- Use short-lived access tokens (5–15 minutes)
- Store refresh tokens securely
- Rotate signing keys
- Implement MFA for privileged users
- Audit all authorization decisions
Security is not a feature — it is an architectural requirement.
Final Architecture Summary
A production-grade system follows this order:
- User authenticates
- Identity verified
- Access token issued
- Token validated per request
- Authorization enforced per resource
- Action logged for audit
Authentication confirms identity. Authorization protects resources.
Both must be implemented correctly to build secure, scalable applications.
